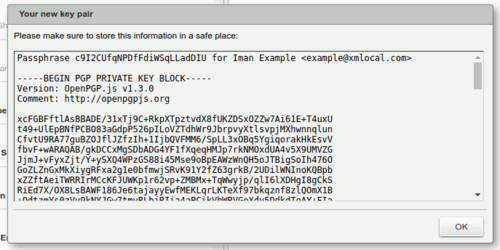
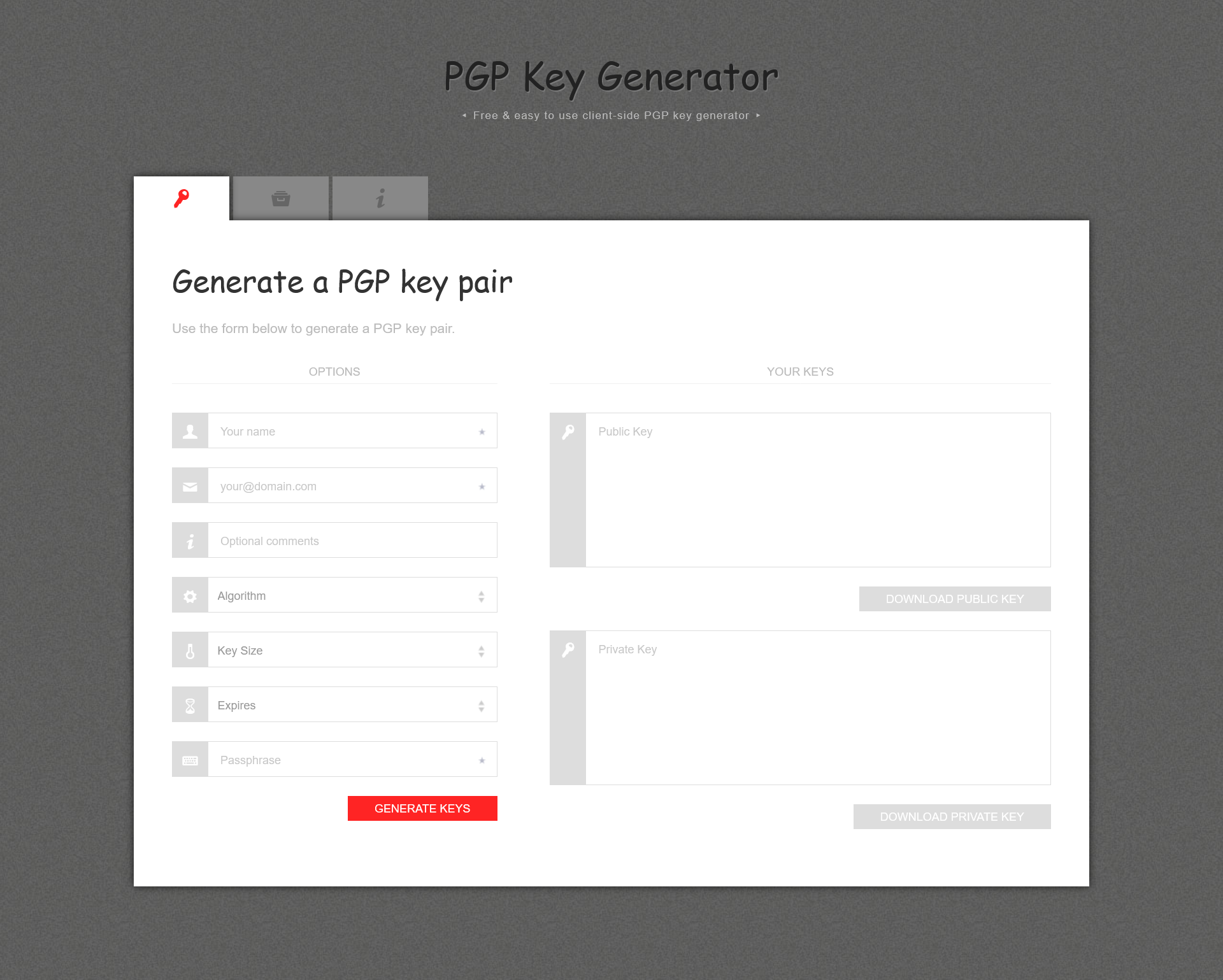
PGP key pair generation and encryption and decryption examples in Python 3 | by Almir Mustafic | Medium
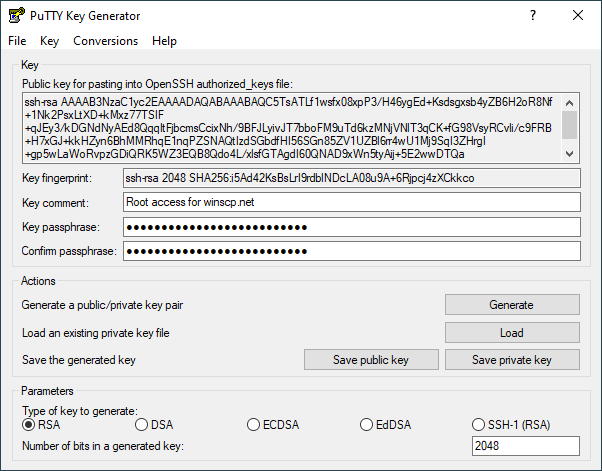
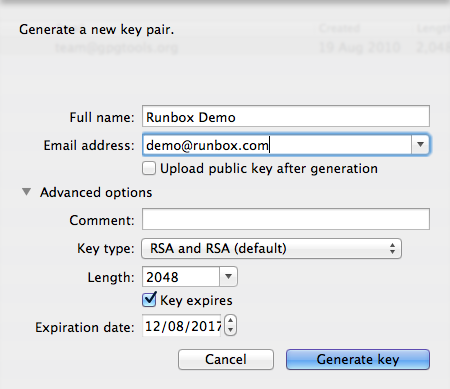
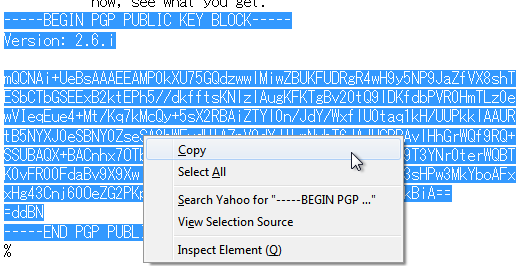
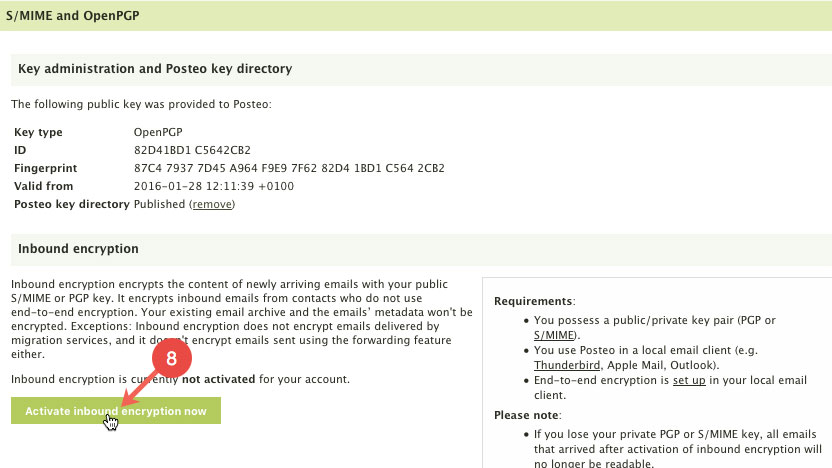
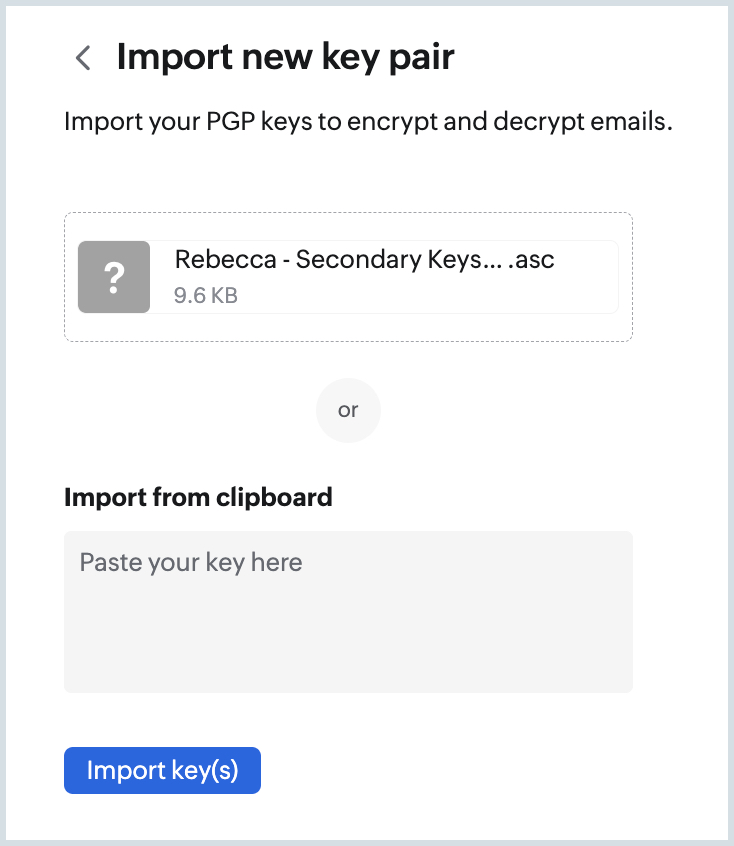
How To Make a PGP Keypair using GPG and Communicate In Absolute Privacy (Linux/Mac) Public & Private Keys + Encrypt & Decrypt Messages - Sick Codes - Security Research, Hardware & Software
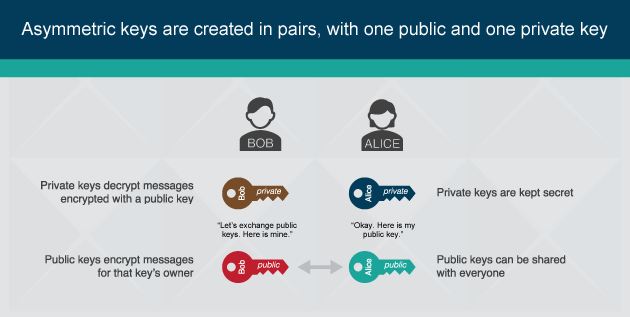

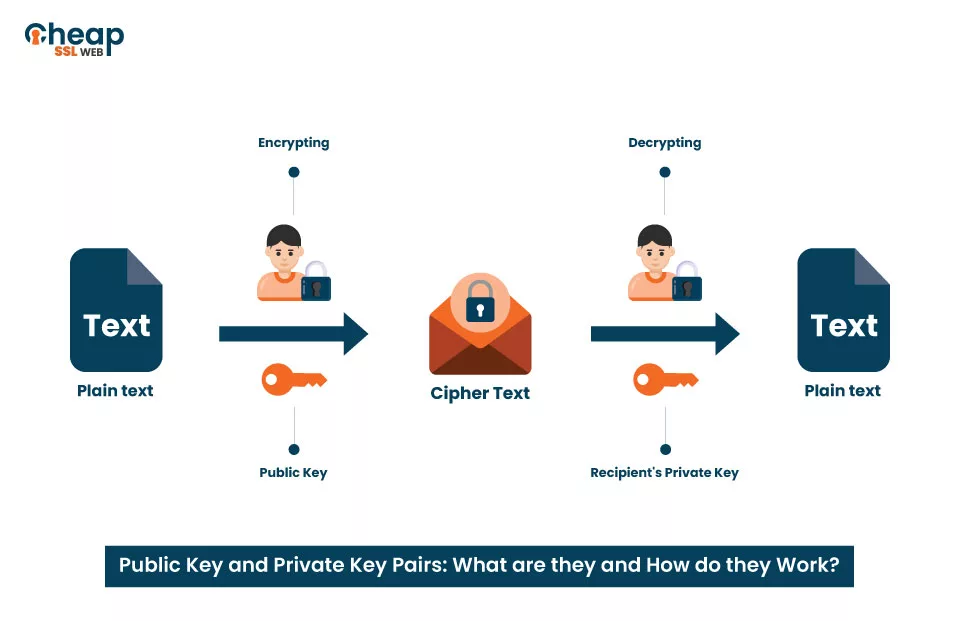



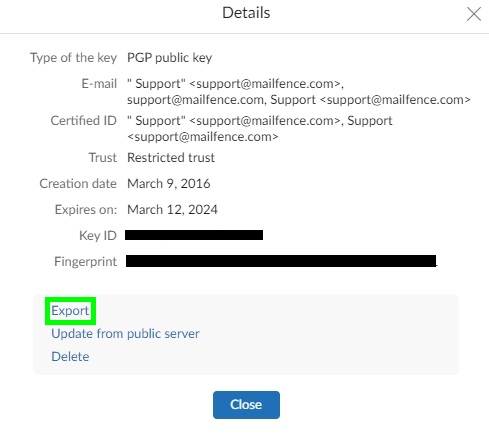



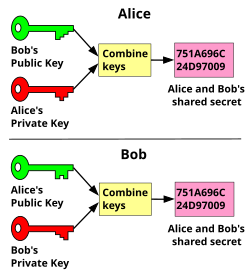
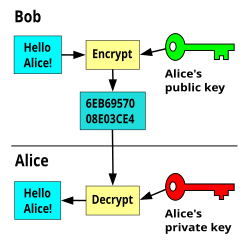
![Tutorial] How do PGP keys work - Jacob Riggs | Blog Tutorial] How do PGP keys work - Jacob Riggs | Blog](https://jacobriggs.io/blog/app/web/upload/misc/pgp-encryption-diagram.png)