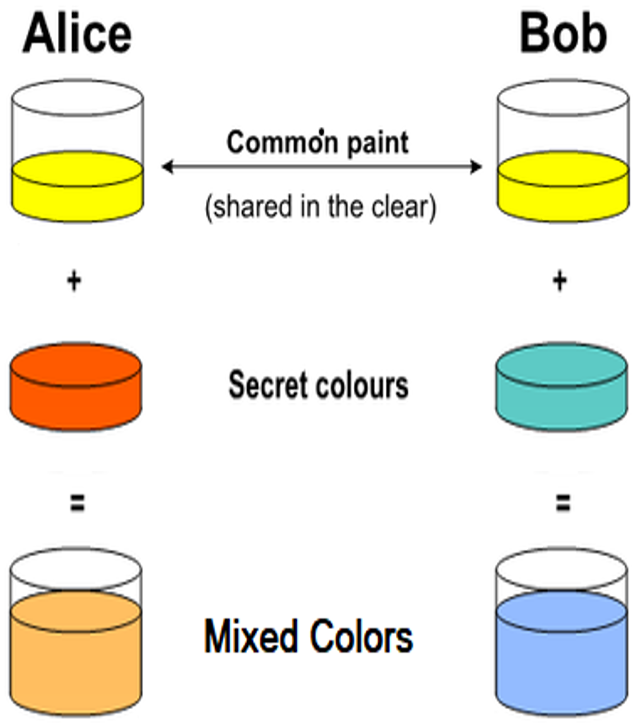
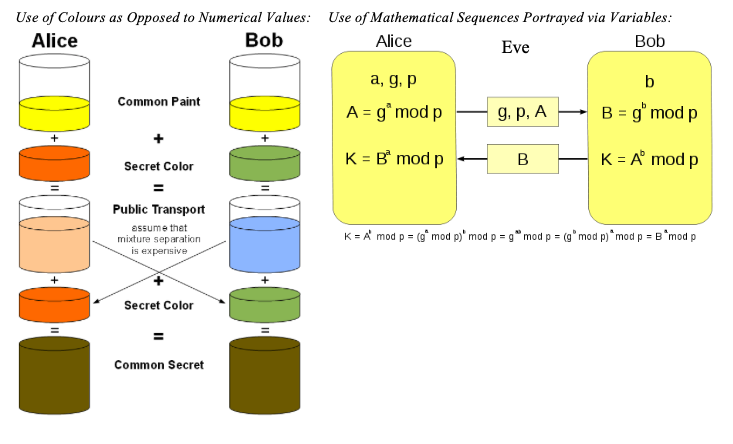
wireless - Is this a correct DH key exchange over RSA wirelessly? - Information Security Stack Exchange

The ECDH key establishment process. The ECDH key establishment process. | Download Scientific Diagram
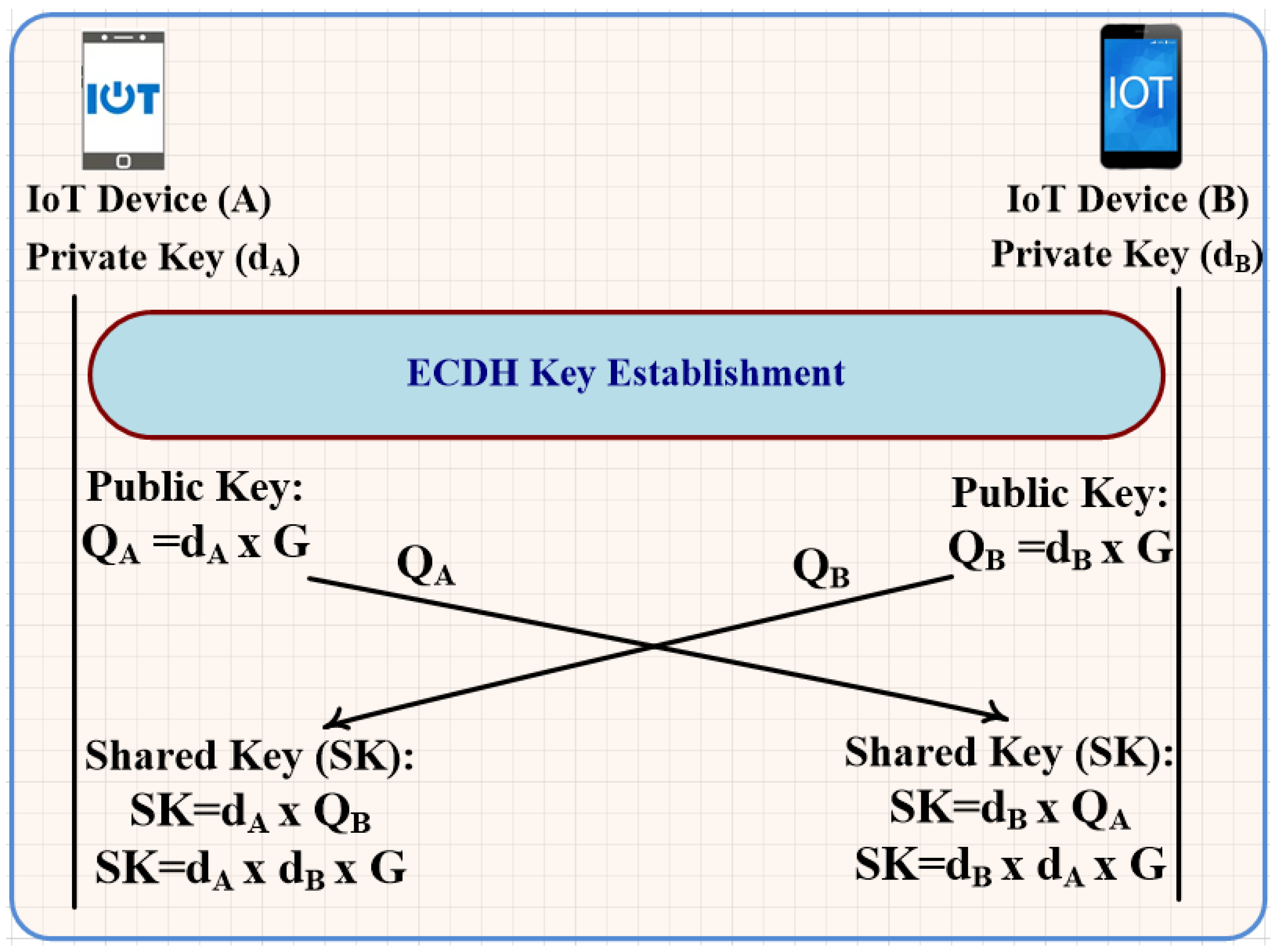
Processes | Free Full-Text | Unforgeable Digital Signature Integrated into Lightweight Encryption Based on Effective ECDH for Cybersecurity Mechanism in Internet of Things

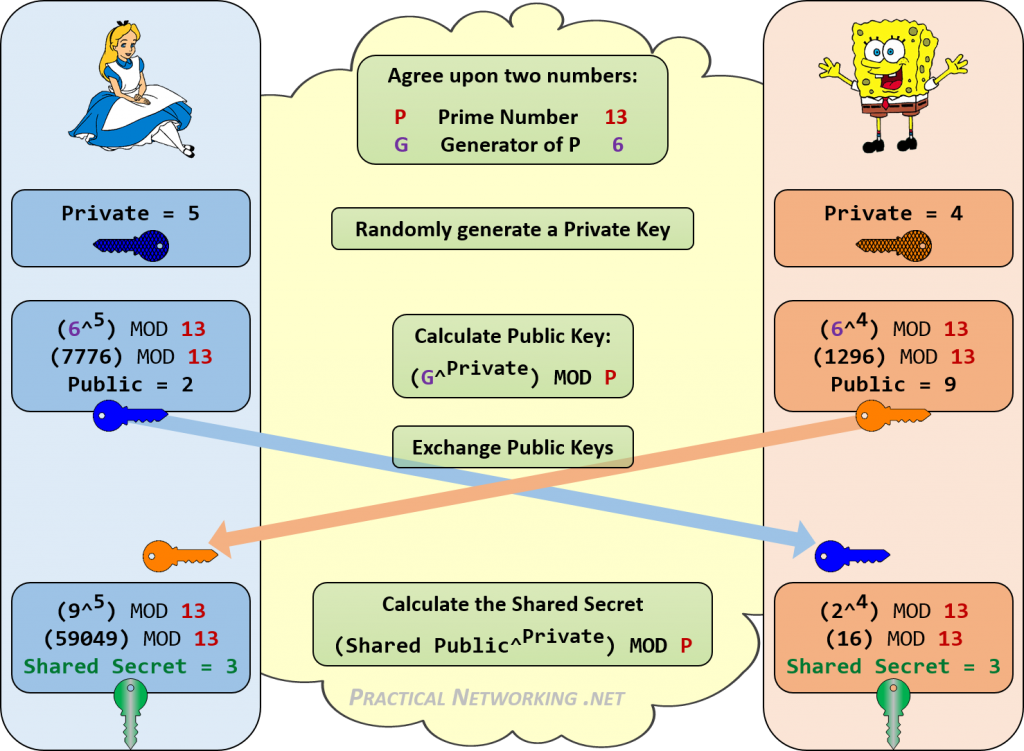
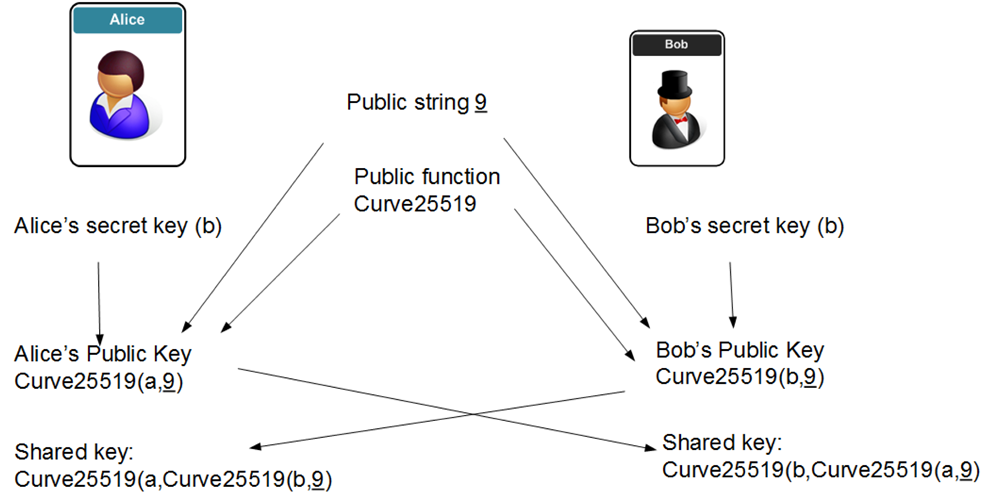
Authenticated ECDH In Python using X25519 | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium

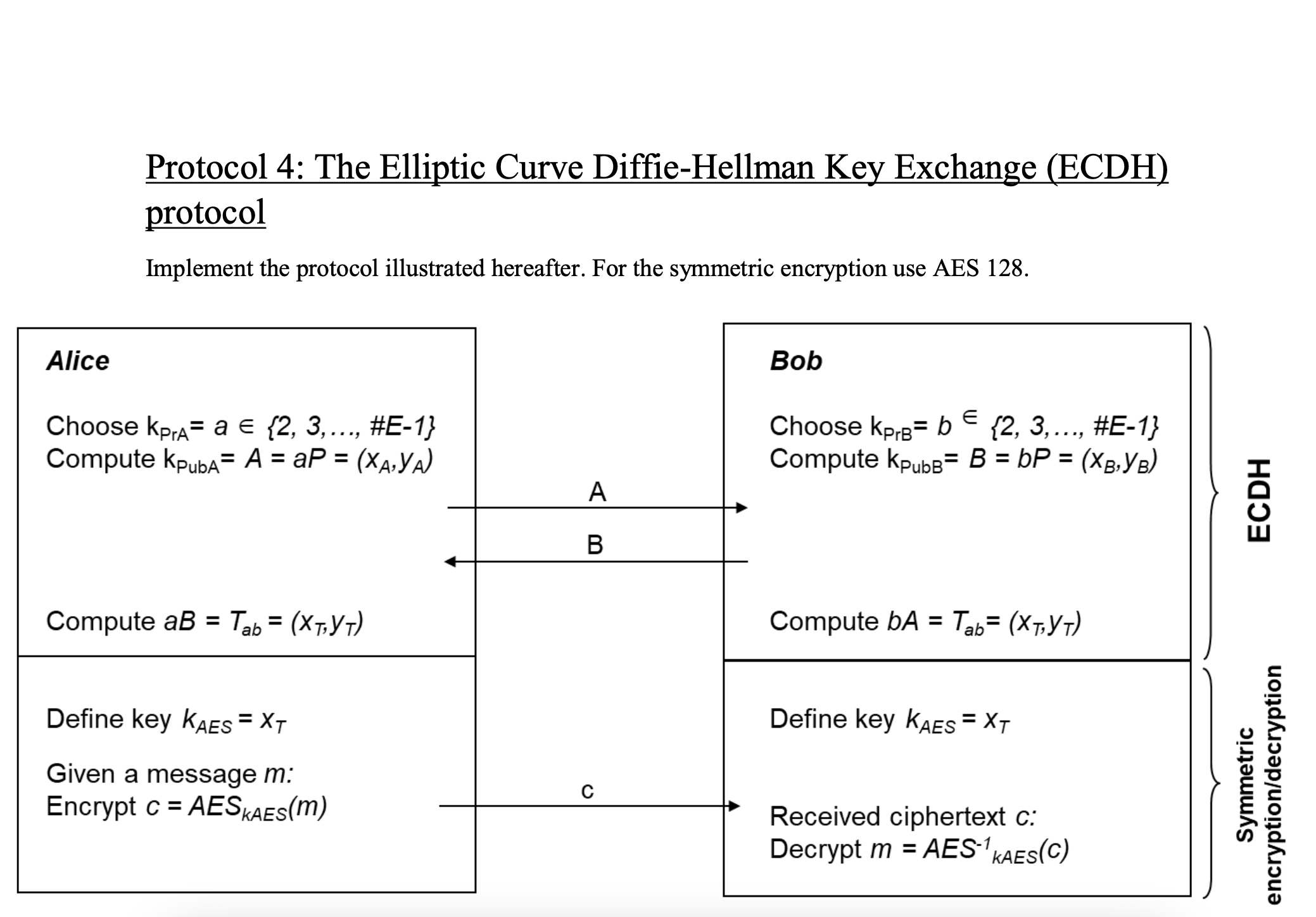
Elliptic Curve Diffie-Hellman (ECDH) Key Exchange Protocol. Two users,... | Download Scientific Diagram

Performance analysis of point multiplication algorithms in ECDH for an end-to-end VoIP network | Semantic Scholar
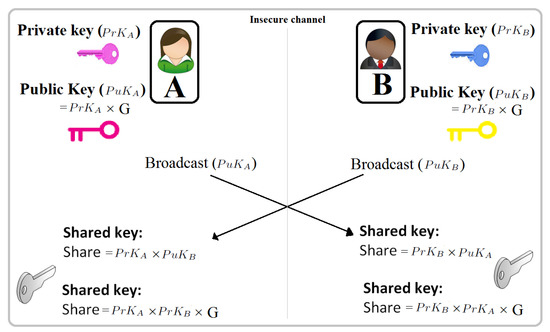

![PDF] The Elliptic Curve Diffie-Hellman (ECDH) | Semantic Scholar PDF] The Elliptic Curve Diffie-Hellman (ECDH) | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/de032e79b6116aeb3efc26de258903d6fdc24a08/1-Figure1-1.png)